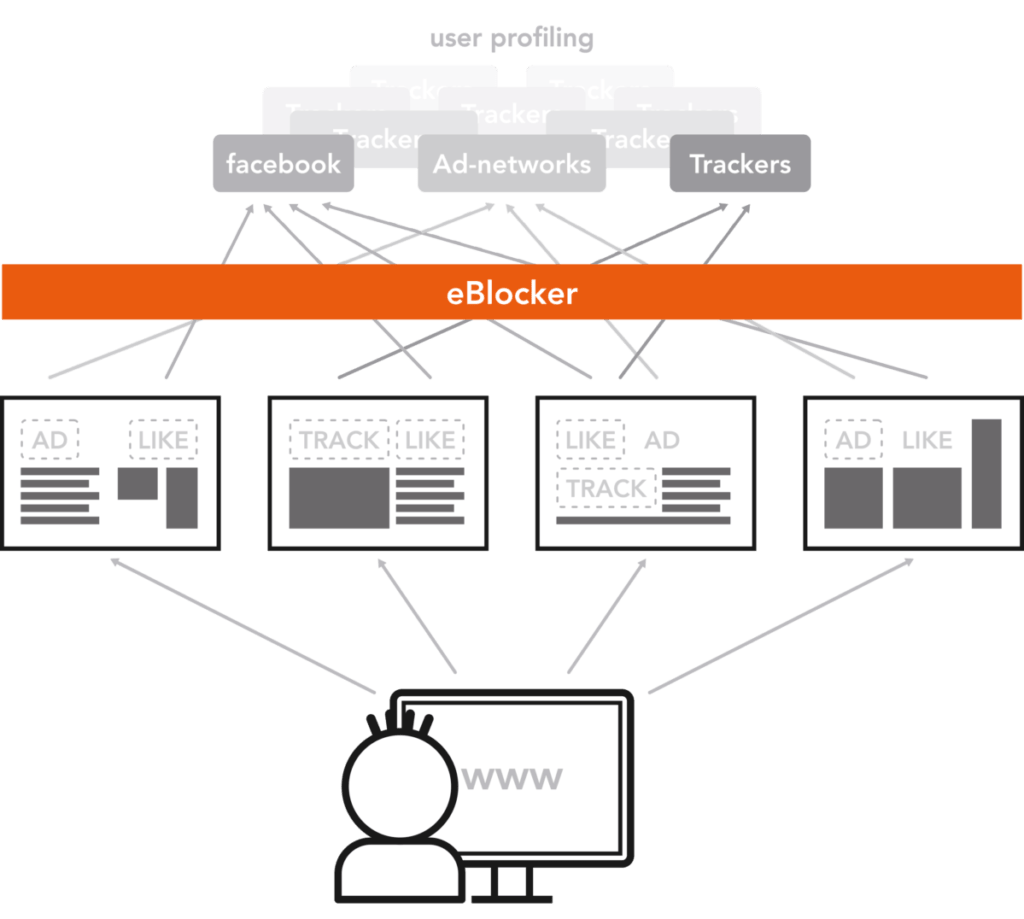
How eBlocker works.
Data traffic is redirected.
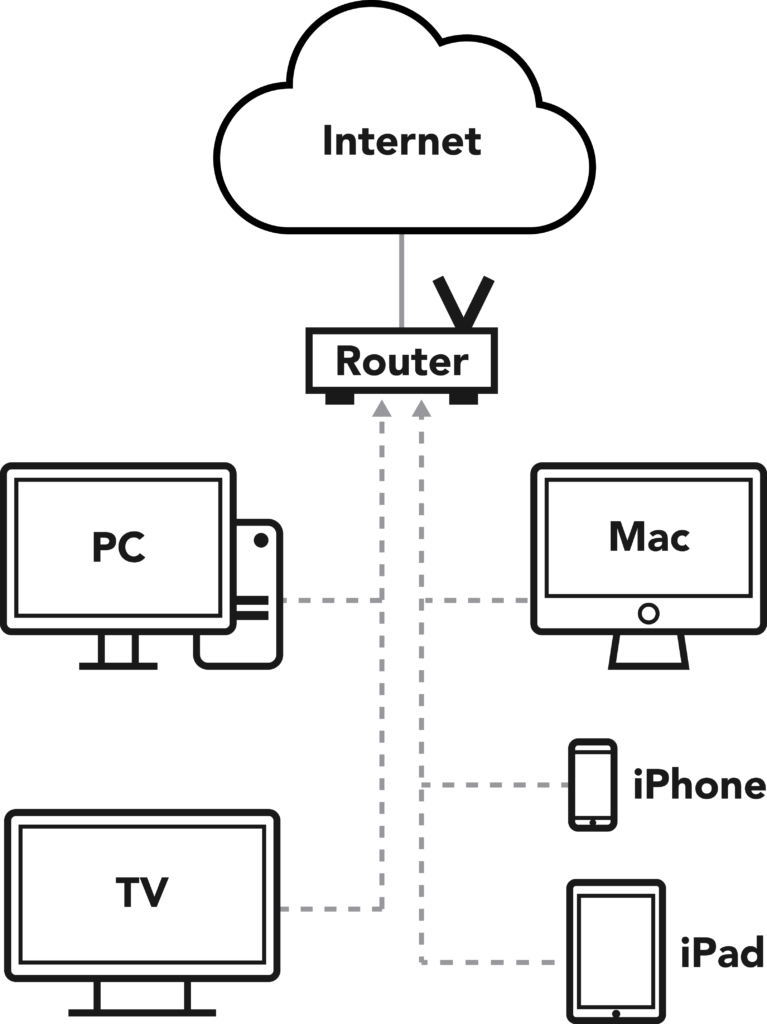
Immediately after connecting the eBlocker, all home network devices send the data packets to the eBlocker instead of the router. Without any software installation: Just plug & play.
Technically explained
eBlocker uses ARP spoofing to act as the gateway for all TCP/IP traffic.
Alternatively, you can configure eBlocker as the gateway yourself or use the eBlocker DHCP server.
Without ARP and fully under your control.
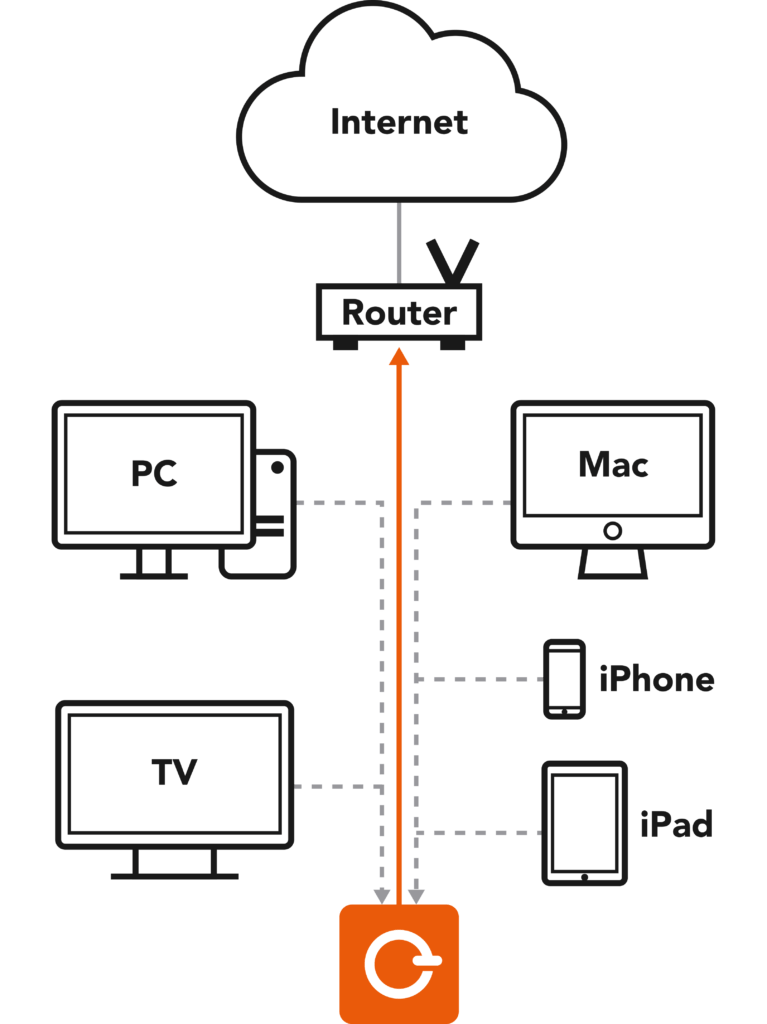
Data packets are checked.
eBlocker checks all data packets and recognizes data collectors, ads and malware based on patterns. Prohibited connections are automatically blocked and you are protected.
Technically explained
eBlocker uses SSL bumping with a unique root certificate to decrypt possibly encrypted TCP/IP packets. After this deep packet inspection a pattern matching to the target URI is performed. In case of a match, the request is answered by the eBlocker (instead of being sent to the target URI).
As a slightly less accurate alternative, eBlocker uses DNS blocking for fallback, where the domains of known data collectors are blocked. This way, even devices that do not allow to install root certificates are also protected.
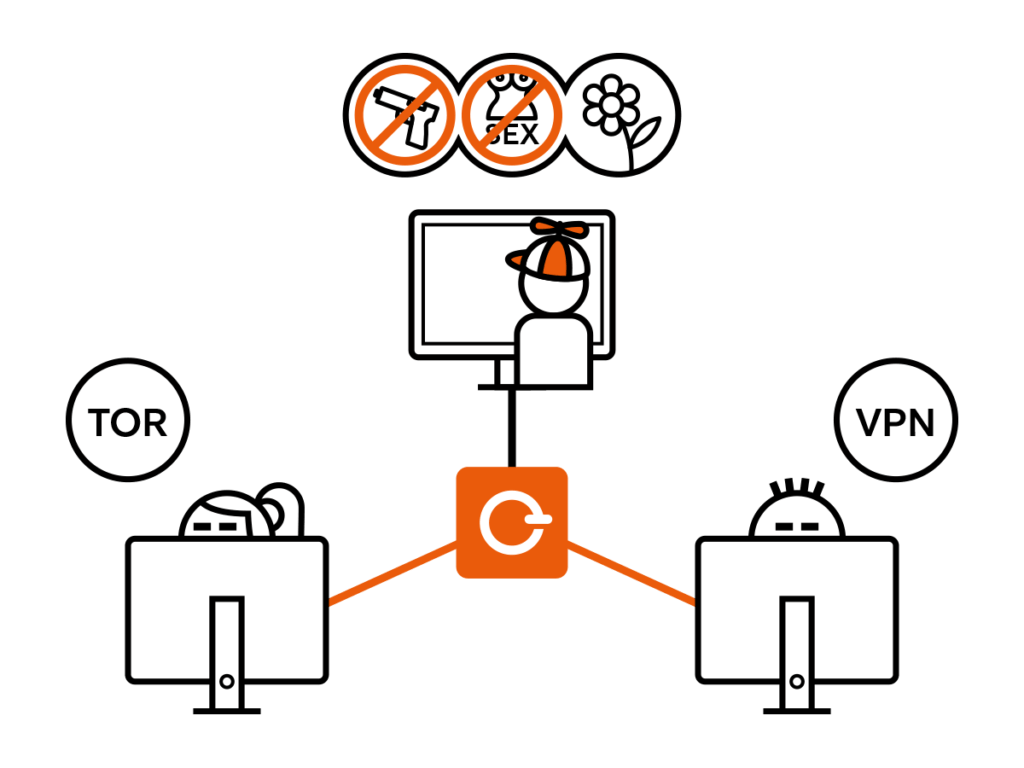
IP address is anonymized.
Your eBlocker can anonymize the traffic of any device. To do this, eBlocker routes the packets of the chosen device through either a VPN (Virtual Private Network) or the Tor anonymization network.
Technically explained
eBlocker can route the TCP/IP traffic of each device individually. Either via Tor (exit-node selectable) or via any OpenVPN capable provider. The devices can also use different VPN providers in parallel.
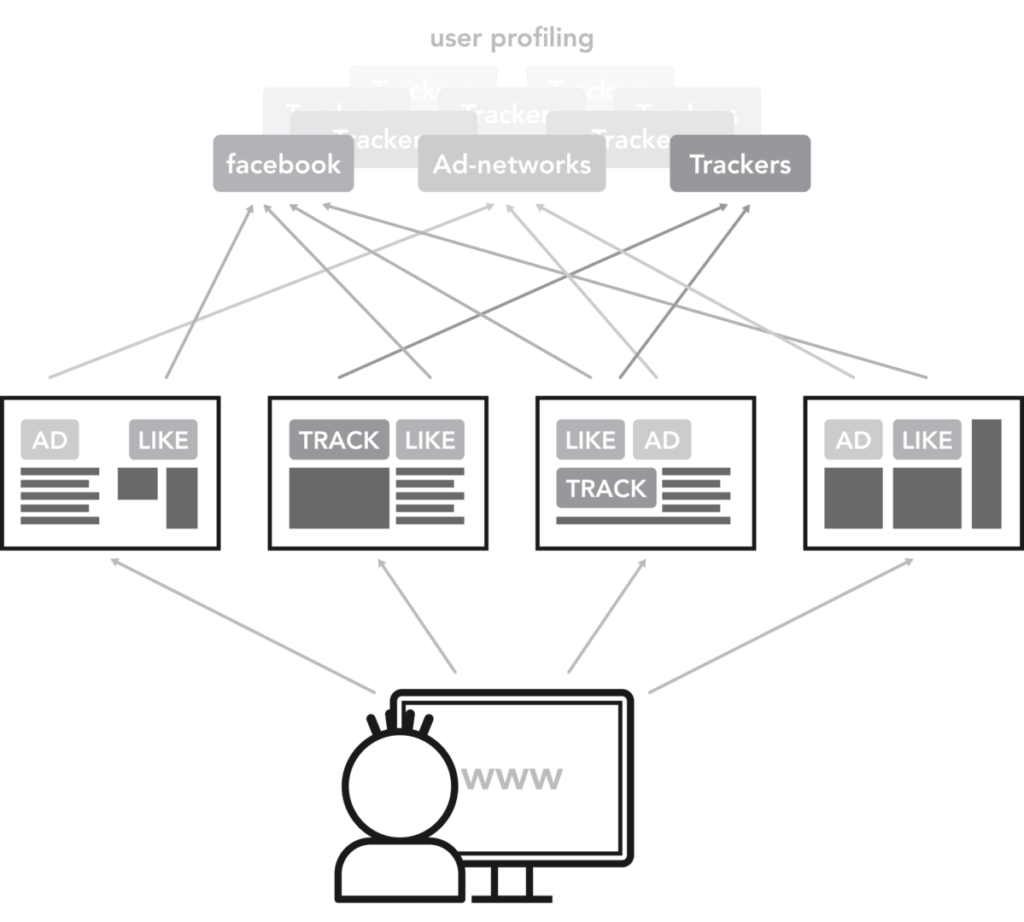
Device is cloaked.
Every device and browser automatically sends a device ID to the websites you visit. This allows websites to optimize their content for specific devices. The device ID also provides information about the surfer’s purchasing power and can be used for fingerprinting.
eBlocker cloaks this ID. So your expensive iPhone looks like a Linux machine – at least for the server 😉
Technically explained
eBlocker can modify the user agent of outgoing requests. You can choose from predefined strings for the most common devices and browsers or set any string yourself. The assignment of the outbound user agent is done individually for each device.
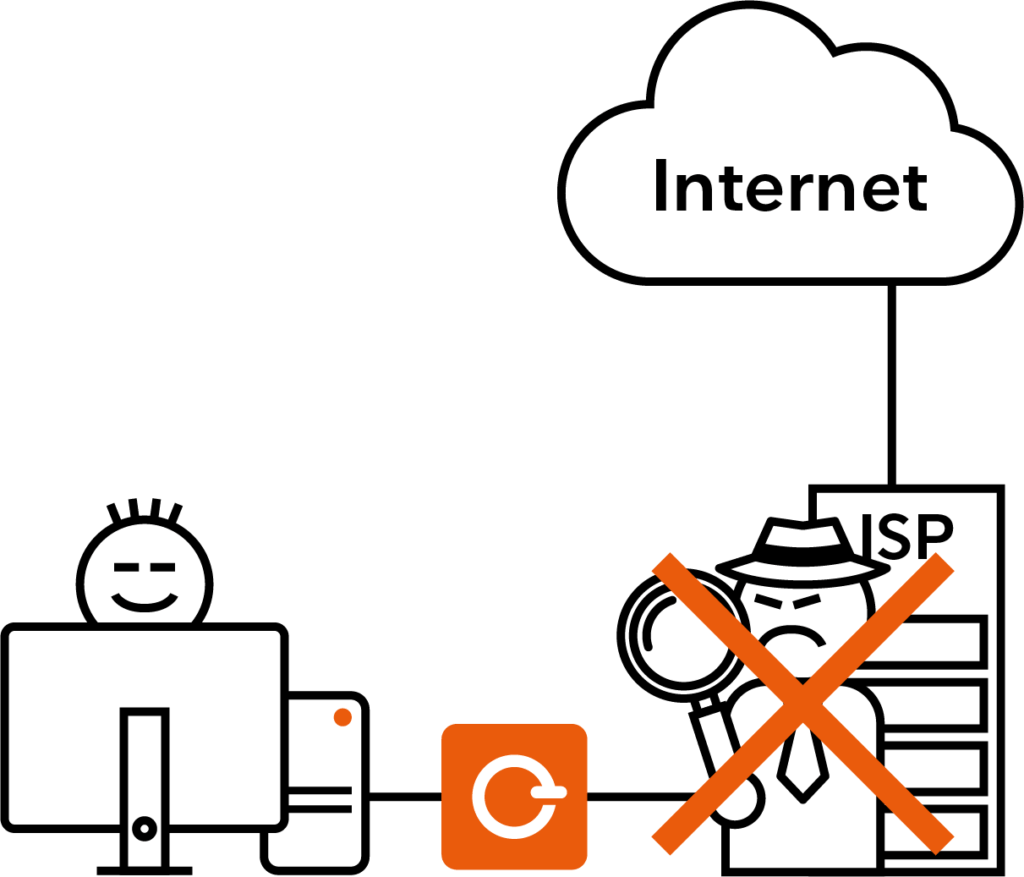
Domain queries are hidden.
Each domain address is converted into an IP address by the so-called Domain Name Service (DNS) of your provider. As a result, every domain you are accessing is visible to your provider – and can be logged and analyzed on a personal level.
eBlocker prevents your provider from logging DNS requests and thus your surfing behavior. So you are invisible even to your provider DNS.
Technically explained
eBlocker runs its own DNS server. It can distribute the requests to different DNS servers of your choice, so that no single DNS receives all requests. The DNS of the provider is not used.
In addition, DNS queries can also be encrypted over the Tor network, even if the regular traffic is not routed through Tor.
In both cases, the ISP will no longer receive DNS queries.
Children are protected.
eBlocker protects children and minors from accessing undesirable content. Depending on the age, the entire Internet can be blocked and only certain domains can be allowed. Alternatively, only certain content, such as pornography, violence or gambling, can be blocked.
At the same time, Internet time can be restricted across all devices according to time and duration of use. Per “Internet off” the parents always have the last word 🙂
Technically explained
eBlocker contains a comprehensive user management. Each user can be assigned his devices and an individual protection profile.
Protection profiles consist of both time and domain specifications, which can be composed of predefined and custom domain lists.
In addition to predefined domain lists of the German Federal Review Board for Media Harmful to Minors, eBlocker contains extensive curated content categories for all areas of the Internet that are permanently updated.