Version 2.6 released
After about four months of development, we released the update to eBlockerOS 2.6 in the night of 03/19/2021. Users who already use eBlockerOS 2.5.x and are using automatic updates have already received the update. The update can also be installed manually via Settings> License&Update> Update> Manual update. Users who still use an older eBlockerOS version <2.5 have to update to 2.5 first to get the newest features.
Besides numerous security updates in the underlying Linux operating system, many improvements and new features have been integrated.
Cookie banner goodbye
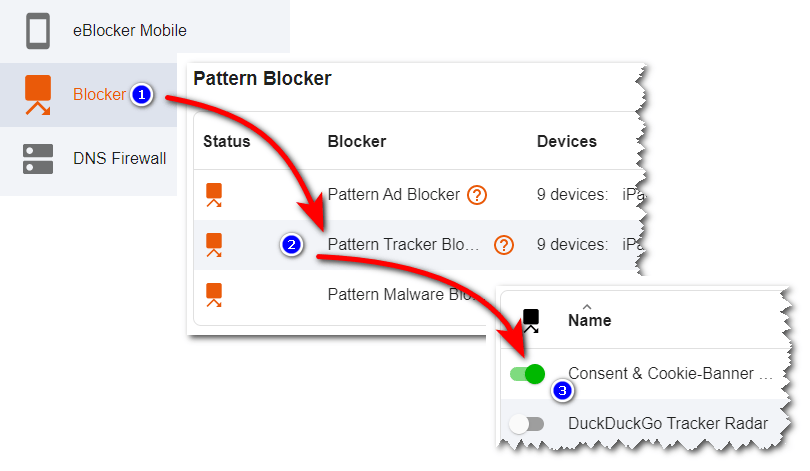
After extensive testing we have now released a new blocking list for cookie banners. It prevents the often annoying cookie consent and makes surfing the web more fun. To use this blocking list you need to activate the corresponding list as shown in the following screenshots:
Important hint
If a website does not work properly due to the cookie banner blocker or it is not accessible due to an ad blocker detection, you can simply pause the eBlocker by clicking on “Pause” in the dashboard or in the control bar. Then reload the page and confirm the cookie banner. Afterwards you can end the pause – and usually you will get directly to the website without being asked again in future. Of course the eBlocker still blocks all data collectors.
Sharper DuckDuckGo Tracker Radar Blocker
Also new is the DuckDuckGo Tracker Radar Blocker, which we have developed based on the public raw data of the DuckDuckGo search engine. The search engine provides us with “suspicious cases” of URL patterns that are used on many websites and can potentially be used for tracking. From this, we algorithmically generate the new blocking list, which is automatically updated daily.
We recommend activating DuckDuckGo Blocker only to users who have particularly high requirements for tracker protection.
Unlike the eBlocker lists we curate, where we aim for a compromise between the protection level and the operability of most websites, the DuckDuckGo Blocker already blocks suspicious cases. Among them, for instance, are so-called content delivery networks, which are used by many international websites for worldwide load balancing. Therefore, with the DuckDuckGo Blocker, some websites will not work at all or only to a limited extent.
Ad hoc filter
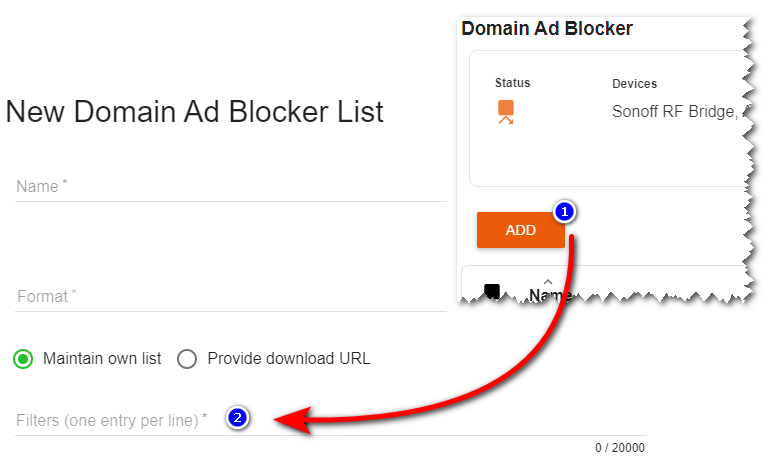
Until now, arbitrary URL sources could be specified for additional blocking filters. Thanks to another improvement, eBlockerOS now offers the possibility to enter blocking lists “ad hoc” directly – without a URL. For this purpose, the domains to be blocked or the URL blocking patterns can be entered directly into the corresponding text field, if the option “Maintain own list” is selected. You will find this option after adding a new blocker:
Hint
To use your own patterns, you can find the definition of the so called Easylist format here, which is also used by the eBlocker.
Improved memory management and user interface
Especially for devices with 1 GB memory, like the “white cube” eBlocker, we have improved the stability when there is only little free memory available. In addition, the speed for devices with more than 1 GB of memory has been increased, as now several work processes can run in parallel. The user interface has been revised in various places to ensure even easier operation.
Raspberry Pi 3 “reloaded”
After a Linux kernel bug was fixed, the Raspberry Pi 3 is now fully supported again and it should not freeze anymore. If you are using eBlockerOS on the Raspberry Pi 3, we appreciate your feedback about the new version in this forum post.
Experimental feature: Auto Trust App
To improve HTTPS compatibility with apps, we are currently testing a new approach: the Auto Trust App. This detects errors when establishing HTTPS connections and automatically sets the domains where connection errors occurred as a trusted app. This feature is in the experimental stage for further development and is not yet intended for production use.
We strongly recommend enabling this feature only if you are a software developer and know exactly what you are doing.
To enable the feature, three prerequisites must be met:
- The recording of HTTPS connection errors must be enabled (Settings> HTTPS> HTTPS connection errors).
- HTTPS error analysis must be enabled for all devices with apps (Settings> Devices> “Select device” – then enable error analysis under HTTPS)
- Enable the Auto Trust App (Settings> HTTPS> Trusted Apps> Enable Auto Trust App)
Important note: The Auto Trust App will unblock domains that may contain trackers or other malicious content. This is known and the current experimentation stage is precisely to eliminate such issues. Please do not enable this feature if you want to be fully protected.
Release notes and image download
The full release notes with all changes can be found here. You can download the eBlockerOS image here.
